Yes fake is good ! because, privacy and anonymity is our digital right.
Everyone should know about the cyber crime and cyber security to protected their information from being hack.
So the Legitimate action is necessary towards this unpredictable censorship.
Hoping to convince or threaten the target/user. As something unusual happens which is not expecting. Scammers are Everywhere so at least use your common sense Like what’s website content or shopping site expecting from you. Beware before giving your personal Detail like email, address, phone number and SSN kind of information online. Never use auto-save or password save option. Always use updated firewall protection and also block advertisement form every device.

…Because I respect your desire for privacy ! poof
Random Identity generator 
fakenamegenerator, datafakegenerator, fakepersongenerator, fakedata, bestrandoms,
 thispersondoesnotexist (system generating random people’s faces based on the StyleGAN algorithm from NVIDIA, as well as software from NVIDIA CUDA. This is a pre-trained model with an excellent interpolation and unraveling system, capable of finding hidden factors of variation (for example, determining the position of a face, identity, and even more than 100 parameters)
thispersondoesnotexist (system generating random people’s faces based on the StyleGAN algorithm from NVIDIA, as well as software from NVIDIA CUDA. This is a pre-trained model with an excellent interpolation and unraveling system, capable of finding hidden factors of variation (for example, determining the position of a face, identity, and even more than 100 parameters)
ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤ
masking email 📬
use tempr.email, Tempmail, Mailnesia, Guerrillamail, tempinbox burnermail Extension, myTrashMail, Mailinator. or check this page – secure-e-mailing
ㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤ
masking keylogs 
KeyScrambler by QFX Software, Ghostpress, GuardedID
Zemana AntiLogger, protectedtext, SpyShelter, Oxynger KeyShield , 
ㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤ ㅤㅤㅤ
masking location or GPS /Fake location/mock location/ teleporting
Use location mocking app for android. If you want to mock your Location you can change it using android developer option. go to developer option and enable debugging option. and select mock location app/ debug app that you installed. all 3 factors are affecting Latitude, Longitude and altitude.
In iPhone & mac go to privacy option and block/ Untick all location options.
Mobile Location Analytics Opt Out – https://smart-places.org



ㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ
Masking phone
simply use some apps like which provide free VoIP number Like textnow, telos, talkU, dingtone, Free Tone, Spoofbox, CoverMe, Line2 , Hushed , Sideline , burner app, inumbr and List goes on. but one thing that you have to keep in mind that area code and number sequence should be Valid.


ㅤㅤㅤㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ
Monitoring/ Spying Software
ㅤㅤㅤ ㅤㅤㅤ ㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ
ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤ
Masking cards/ masking wallets
The purpose is to mask your credit card is protect you from data breach. Your real credit card details aren’t revealed during these transactions, which provides an extra layer of security. This is similar to the virtual phone number service we talked about previously.
so the next time you need to make a purchase, you get another one-time use credit card number.

Here is some site which provide masking card service but some of them are not free or you have to pay for them.
🔗 https://ezzocard.com/
🔗 https://privacy.com/
🔗 https://myshadow.org/
🔗 Crypterium Virtual card visa connect to ApplePay and get ready to pay anywhere, anytime
🔗 https://www.abine.com/
🔗 https://www.revolut.com/en-US/revolut-premium
🔗 https://www.netspend.com/prepaid-debit/features/virtual-cards/
🔗 https://www.capitalone.com/applications/eno/ – Eno® from Capital One extension
🔗 https://money.yandex.ru/cards/virtual
🔗 https://www.americanexpress.com/us/payment-solutions/amex-go-virtual-cards/
🔗 https://www.skrill.com/en-us/
ㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ
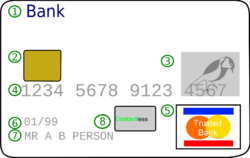
Credit card / debit card complete Structure


Carding is a type of fraud in which a thief steals credit card numbers, makes sure they work, and then uses them to buy prepaid gift cards. The fraudster may sell the prepaid cards or use them to purchase other goods which, in turn, can be resold for cash.
ㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ
Secure your card/ how can you avoid it?
– Don’t share your Card CVV number or erase it from the Card & keep this in your mind
– Multifactor authentication (MFA) and 3-D secure way of payment. never use auto-save. cleanbrowsing
– Use virtual keyboard or Key masking application Like Keyscrambbler.

ㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤ ㅤㅤㅤㅤㅤㅤㅤㅤㅤ
How Truecaller work ? How he knows your friends mother name ?
“True Caller is a global directory containing millions of phone numbers that have been sourced from public directories, yellow pages and crowd sourcing techniques. “One of the techniques used by True Caller to grow its vast database of numbers is to opt in crowdsourcing. In other words, whenever someone installs the app on their phone, they have the option to enable something known as Enhanced Search, which will allow True Caller to upload all entries from that mobile phone’s address book to their global database. By installing True Caller, your entire address book becomes a part of the publicly searchable True Caller database, without the permission of the people who own those numbers.
This article is regularly updated for relevance. ![]() admin
admin

